The Windows Insight repository now hosts the Windows Telemetry ETW Monitor framework. The framework monitors and reports on Windows Telemetry ETW (Event Tracing for Windows) activities – ETW activities for providing data to Windows Telemetry. It consists of two components:
- the Windbg Framework: a set of scripts for monitoring Windows Telemetry ETW activities. The scripts are fed to a running windbg instance, connected to the Windows instance whose Windows Telemetry ETW activities are monitored.
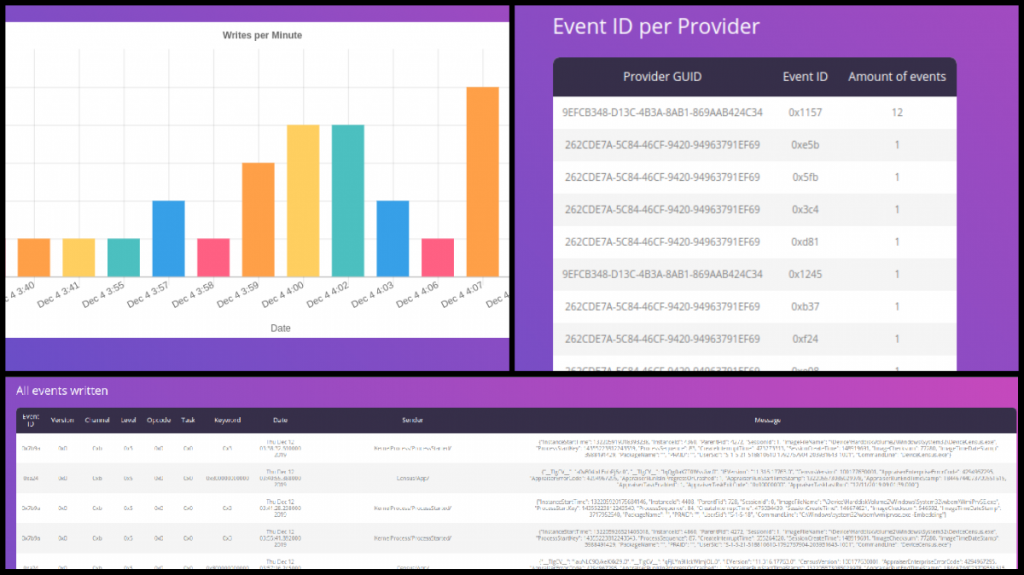
- the Telemetry Information Visualization (TIV) framework for visualization of information and statistics. The TIV framework is a set of Python scripts that visualize information and statistics based on the data produced by the Windbg Framework. The output of the TIV framework is a report in the form of a web page.
The Windows Telemetry ETW Monitor has been tested on Windows 10, version 1909.
Continue reading “Windows Insight: The Windows Telemetry ETW Monitor”
Continue reading