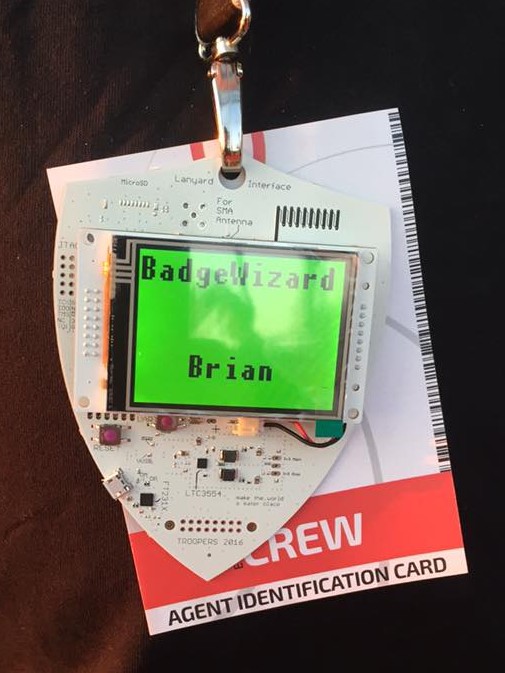
Real men used to wear pink pagers, but that’s the past and recently it was time for Troopers 16. Meaning: Real Troopers wear awesome Badges! And, from the feedback we got, they did!
Troopers might be over, but the era of the TR16 Badge is seemingly just beginning. As such, here’s a quick insight into the badge!
To start, this is the first of (at least) three blogposts covering the badge. As we’re currently in the middle of stripping and cleaning our source code repository, this post now will not cover the firmware. The stripping is not about hiding something, but as we used an Open Source RTOS our repo currently contains modules, which are for completely other architectures.
In addition we needed a few workarounds while getting the badge up and running for the conference, following our own hacking sessions, there will be a dedicated post concerned with hardware modifications and hacks which can be performed.
The Introduction
As some of you might know, for quite a while a little pink girl’s toy made its name throughout the community: The IM-ME. Having been designed as an embedded chat client with software and a dongle on the parent’s PC, it protected girls from chatting with strangers. With the backend network having been shut down and the devices being dumped on eBay a few hackers gave them a try! Turns out they’re portable, small, reprogrammable but sadly also hard to get and slow!
Now came we: grabbing a streamlined ARM Cortex M3 processor, with an M0 RF core, a simple touch display and a bunch of Troopers magic and spirit we designed the sweet little gadget you’ve been playing with for the past few days.
The Story Behind the Badge
In August Mike Ossmann had come to visit us, for a quick hacking session, and with him he brought us a few HackRF One and an IM-ME. As already said, the IM-ME is a kids toy, with loads of potential, but a few down sides. Having had this little device on my mind since this day, I’d been roaming the Internet, looking for a creative way to actually have both an IM-ME style badge and also make the first step into creating a neat little RF platform for the community. Then last spring, Texas Instruments announced the CC1310 as the successor of the CC1110 which had been used in the IM-ME. Reading the specs and the RTM date of Q3/15, I decided to put together a quick sketch, collect some numbers and the preliminary results looked good!
After a few more chats with Mike and my fellow BadgeTeam guys Chris, Stefan and Olli, we started waiting for the delayed RTM and our ordered samples……**Please insert a story of friendship, inspiration, love and magic here**
Now, less than 5 months after first access to the chip, here is the TR16 Badge
Bill of Big Materials
- The RF SoC containing both the M0, the M3 and the RF module: CC1310
- The Display: MI0283QT by watterott electronic
- The USB to serial converter: FT231x
- The DCDC Converter: LTC3554
- The PCB: Custom schematics and layout!
As already mentioned the CC1310 was a bit of a premiere. We only received our first samples in November,so a lot of our prep work was completely theoretical, with loads of guessing and abstractions from the CC26xx chip range, which is based on the same core. Also our Schematics were based on preliminary information. All this resulted in quite an odyssey which we only managed with the help of a few friends (more on that later on!).
Technical data
- CPU: 48MHz ARM Cortex M3
- Flash: 128KB
- RAM: 20KB
- Supported RF-bands: 315-, 433-, 470-, 500-, 779-, 868-, 915-,and 920-MHz ISM and SRD
- JTAG & serial bootloader
- Real Time Clock
- “True Random Number Generator”
- AES-128 Module
- OTA capability
- Integrated temperature sensor
With these specs, the CC1310 offers a very very large potential, and seemed just right for a conference Badge, which would actually also contribute to future research.
On the Badge the CC1310 is equipped with a PCB helix antenna, which can be seen in the top right corner of the badge. If needed, one can disconnect the PCB antenna, and populate the footprint for an SMA connector. Both receiving and transmitting data with the badge are possible and will be included in the planned source code release. For the conference, we decided to stick to the receive function.
Although the chip does sadly not contain a USB interface, it comes with a serial bootloader, which is exposed by the used FT231x. By adding the serial to USB bridge, we made flashing via USB possible – there is a simple python script, which can push new firmware images to the badge. At the same time, the FT231x is used to make talking to the Badge possible. When connected to USB, a serial interface will be added to the host computer, so that one can access the Badge with a terminal like (minicom, putty). If you’re going to give this a try, you will have to enable carriage return in your client!
Software-wise the Badge is running a copy of contiki-os. We went for this approach, as it’s officially supported by TI, and sadly the TI-RTOS was not compatible with our intentions, due to its license. Our contiki branch is based on the the code for the CC26xx and utilizes quite a lot of the already available functions. We will make sure that the changes we made to support the CC1310 will be pushed upstream.
The RF-Interface
During the conference we broadcasted multiple messages to the badges, which were displayed on the screen. As a transmitter we used a YARD Stick One and a simple python script to automate the access to rfCat.
The script will configure rfCat as follows and then simply send data:
d = RfCat()
d.setFreq(868000000)
d.makePktFLEN(30)
d.setMdmModulation(MOD_GFSK)
d.setMdmSyncMode(SYNCM_30_of_32)
d.setMdmSyncWord(0xaabb)
d.setMdmDRate(50000)
d.setMdmDeviatn(25000)
d.setEnablePktCRC()
The complete script will be released with the source code!
Concerning the range, we where able to cover the complete PMA with a single YARD Stick One. When using the badge as a transmitter, a range of 6-8m seems to be running perfectly. Everything above that might need some further optimization.
The Name Change Game
As a you might have noticed, at some point during Troopers, Evil Sergey attacked our Badge setup and changed all the names on the Badges. I’m very happy that many of you took part in the game, found your name-change-partner and had some fun in the process. The aim of the game was to introduce even more socializing into Troopers. Even though Troopers is clearly a family conference, there arealways distant relatives to which you don’t talk very often. Well, I hope we changed that!
Here a few examples of how people found each other:
- “Oh, we’re standing right next to each other!”
- “Hey, he’s in the Troopers GSM phonebook!”
- **Puts up a sign with a name on his table**
- **Goes onto Twitter, tracks down the guy and makes him come back to the venue from the hotel**
Soldering
As you will have noticed, this time there was no soldering challenge on the Badge. During the development process, we made the decision that the Badge ought to run out of the box and should be rather energy effective. The consequence was the lack of soldering options. BUT as soldering, for us and also seemingly you, is a must, we applied a little bit of magic.
As an alternative, we handed out a small soldering kit for a USB condom. The final device will make it possible to connect your mobile phone to a random device, while physically protecting it from the access by host device. How? We cut the data lines! A detailed description will follow in a dedicated blogpost.
The FAQ
Q: My Badge is showing a white screen!
A: Press Reset!
Q: Reset does not seem to help!
A: Press Reset! During the conference, Chris and I evolved to having magic fingers for when touching the badges. Although this might sounds strange, I’m being honest here. The Badge has a glitch with a pull down resistor on the Bootloader pin. Funnily enough, there where multiple situations in which attendees told us, reset didn’t work, Chris or I touched the badges and they were fine again. We do not have an explanation, except for spirit and magic. If reset does not work, press reset again. Sometimes a quick burst of resets will do the job!
Q: How do I charge the battery?
A: Connect it via USB and wait! A red or green LED on the badge should start glowing while the battery is charged. If it doesn’t, connect the badge via USB and the connect the battery to the badge.
Q: I want to my badge to show arbitrary text messages!
A: Wait for the firmware release. We will expose a function via the serial interface, enabling you to simply display a message on the screen.
The TR16 Badge and Its Future
Everybody involved in the badge and also quite a few attendees are of the opinion that the Badge, or rather the design behind it, needs to be extended, optimized and made available to the community for future use.
Hence we and a few others are already working on further firmware and code examples, both to bring more functionality and offer a quick start for you! All this will be aimed at the Badge as you received it during the conference.
Above that, at this point I can tell you, that there is a private project which will eventually bring a modified version of the Badge to a crowd funding campaign and by this will make the spirit of the Badge live on throughout the community. (If you have any questions, feel free to contact me.)
BUT , the big but, this campaign will not start right after Troopers, as we are still having issues with the CC1310 as a chip.In September 2015 TI issued a Silicon Errata, a document on issues which they are still having with the chip them selves. Here is a few details:
- Not supported Frequency bands: At release the CC1310 only supported: 863 MHz to 876 MHz and 902 MHz to 928 MHz.
- Not supported Modulations: At release the CC1310 only supported 2-FSK. 4-FSK, DSSS, and OOK.
-
Not supported Digital Features: At release the CC1310 did not support Automatic listen-before-talk and clear channel assist.
The document states that, for all the mentioned problems, certain testing had been done, but is not yet finalized and the features would be activated by a firmware update. For the Badge, for research, for playing and basic hacking all this is ok. So you can still just grab the Badge, reprogram it and start hacking. But for a long term project, the hardware needs be free from major issues. I will get into contact with TI soon, and will try to create some kind of time line.
What’s next?
We will shortly publish a further blogpost containing the source code and an introduction on how to use it. Above that we will write a another post on a few possible hardware hacks and modifications. That post will also include the complete schematics. The PCB layout will yet again not be released. The reason for this is, that the Badge is an anchor point for memories and kind of a limited edition, as such we do not want to offer the means to copy the design.
The large THANK YOU!
Thanks to all you Troopers, for a legendary week and all the awesome feedback!
As some of you might know the team behind the Badge has grown from being the BadgeWizard to a a little team of four guys at ERNW including Chris, Stefan, Olli and myself. At this point I’d like to personally thank my three Sorcerers for investing a large amount of heart, spirit, sweat, tears and blood. All of us are hackers, and basically the Badge is always the one major hack of the year, for everyone working on the Badge. And yet again, we owned it!
Also a big thanks to Stephan Watterott and his team from watterott electronic for going the extra yard and helping us with our QA rounds and giving us input on everything we might be able to optimize.
Now to the White Knights of the Badge:
Even Sorcerers and Wizards are not invincible to biological warfare and sometimes come down with a cold which f***s up a tight time plan. Luckily, amongst you Troopers, there are many knights, which come by and offer your help. As such I need to thank all of you guys who approached me, asking what could be done, during a dark and sleepless period.
An explicit Thank You goes to the White Knights of the Badge for saving the day:
- Dominic Spill
- Jeff Gough
- Kevin Redon
- Michael Ossmann
- Mike Ryan
- Richo H.
- Rodrigo Branco
- Sergej S.
- Timo S.
Above the knights, thanks to the partners, family and friends which joined in by helping or just keeping us going.
Last but not least, thanks to Enno and Rene, for giving us the chance to create this epic Badge!
Hope to see you all soon!
For the Sorcerers of the Badge,
Brian
The BadgeWizard
Hi Brian,
it *IS* an epic badge and a very cool gadget indeed. Do you know when you’re going to publish more info / source code etc.?
Cheers,
Stefan
Not quite sure, yet. But feel free to give this a try: https://github.com/BadgeWiz/TR16Badge
Thanks for the awesome badge, the great time at troopers and all your passion, love and time invested in it.
Can you give a hint to enable the next level?
Try this:
https://github.com/BadgeWiz/TR16Badge
Hi Brian,
Thanks a lot – now I know what I am going to do tomorrow (bank holiday here).
Cheers!
Stefan
Michael Ossmann mentioned during his talk that he plans to develop a simple radio spectrum analyzer for the badge. That would be really cool! Any news on that?