Some weeks ago, Heinrich and I had the pleasure to participate in the heisec-Webinar “Emotet bei Heise – Lernen aus unseren Fehlern”. We really enjoyed the webinar and the (alas, due to the format: too short) discussions and we hope we could contribute to understand how to make Active Directory implementations out there a bit safer in the future.
Continue readingTag: heise
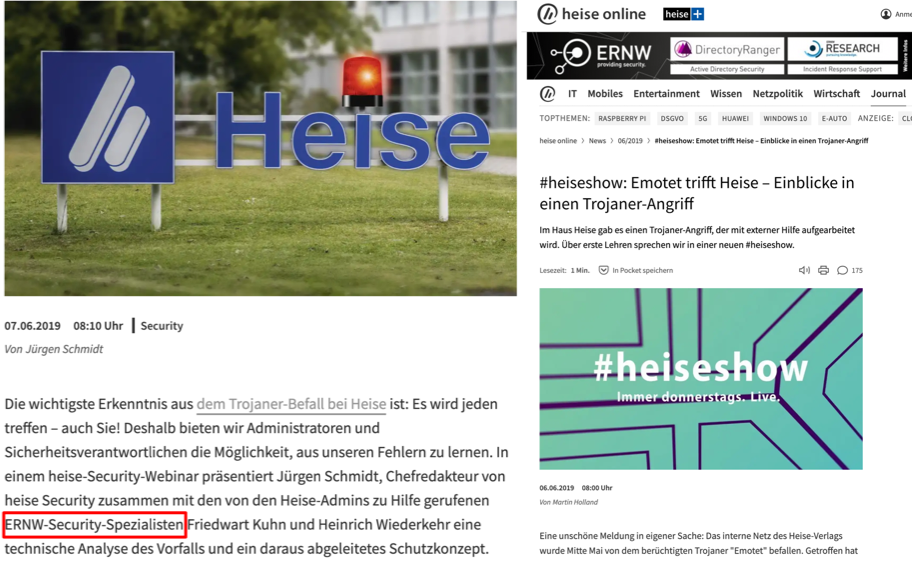
Emotet at Heise, Emotet there, Emotet everywhere – Dissection of an Incident
After the Emotet Incident at Heise, where ERNW has been consulted for Incident Response, we decided to start a blogpost series, in which we want to regularly report on current attacks that we observe. In particular we want to provide details about the utilized pieces of malware, different stages, and techniques used for the initial infection and lateral movement. We hope that this information might help you to detect ongoing incidents, apply countermeasures, and in the best case to figure out proactive countermeasures and security controls beforehand.
Continue reading “Emotet at Heise, Emotet there, Emotet everywhere – Dissection of an Incident”
Continue reading