This week Chris and I participated in the RIPE 78 meeting in Reykjavík. Being part of the group was fun as always and we had quite some interesting conversations with peers from (not only) the IPv6 community.
Big thanks to the RIPE NCC team for the smooth organization and for taking care of us!
In this post I’ll provide some notes on talks I found particularly interesting, plus links to our own contributions.
On Monday we gave a tutorial on “IPv6 Security in Enterprise Organisations”. Here‘s a post with some initial thoughts (I know the sequel to it is still missing ;-)), and the slides can be found here.
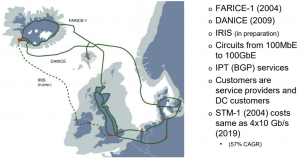
As part of the opening procedure of the meeting & the plenary session Örn Orrason from Farice provided a nice welcome address. While those (addresses) are not always overly exciting I really liked his one, for two reasons: I have a bit of technical interest (as in “little boys love planes and rockets”) in the physical topology of “the Internet”, namely in submarine cables. So this slide had my great sympathy ;-):
Also I learned a bit about Iceland, among others that it pretty much only consumes energy from renewable sources (geothermal power and hydroelectricity).
His slides can be found here and here’s the video.
Later on the day I gave a lightning talk titled “Is 2019 finally the year of Linux on the Desktop? And what about v6-only in WiFi networks?” which essentially was a shortened version of our talk from the #TR19 NGI IPv6 track laying out the results from our testing of 35 applications as for their functionality in a Wi-Fi network with v6-only+NAT64. Slides can be found here and the video is here.
On Tuesday there were two talks which I found particularly interesting (overall there were quite a few good ones). First Brenden Kuerbis and Milton Mueller presented on “Economic Factors Affecting IPv6 Deployment”. While many people sense (and expressed this both on the mic and at other occasions) that the researchers overlook some intricacies of the space I for one think there’s some interesting observations & conclusions in their work (e.g. that some enterprises might feel less pressure to deploy IPv6 as in their case growth is not related directly to the availability of IP addresses, which in contrasts applies to, for example, mobile network operators).
Slides here, video here, full research paper here.
Directly after that Petr Špaček from CZ.NIC and Ondřej Surý from ISC discussed “DNS flag days (plural!)”. The first “DNS flag day” happened just some months ago, on February 1st 2019 (see also here), on the initiative of some major players in the (DNS) field. They had identified certain types of behavior deemed non-compliant with existing standards (namely EDNS extensions, RFC 6891) which in turn led to unneeded complexity and slow processing, so they wanted to send a broad signal “hey operators, from this day on we as a group consider this non-compliant, please adjust your systems, for the common good of everybody using DNS, else you might no longer be able to interoperate with us”, which can be summarized as follows:
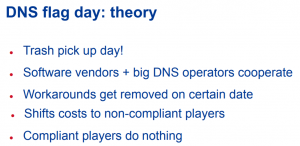
At large they consider the 1st DNS flag day a huge success (as “fixing” occurred without noticeable problems) but they think the overall communication can be improved.
They plan a second flag day for 2020 based on the following motivation:
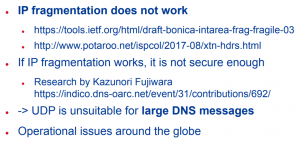
I covered some of the technical background of fragmented DNS responses in IPv6 networks a while ago in this post, and Geoff Huston provided a technical explanation and extensive data in two posts on the APNIC blog (concluding the second one as follows: “[…] maybe we should bow to the inevitable and recognise that, in IPv6, fragmentation is an unfixable problem”).
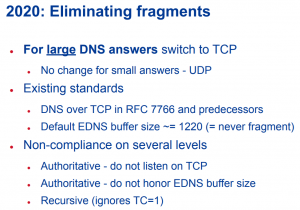
In any case the objectives of the 2nd flag day can be broken down to this (“encourage” the use of TCP and enforce EDNS buffer size of 1220 in order to avoid fragmented responses):
The reaction to their talk was quite controversial; many people heavily criticized the plan. For example Peter Koch from DENIC was sceptical about two points:
- he wondered about the underlying governance model and
- he mentioned that the results of the mentioned research work showing vulnerabilities of fragmentation in the DNS context couldn’t be reproduced.
I have some comments here. One of the authors of the original paper (“Fragmentation Considered Poisonous“), Haya Shulman, presented their results at the #TR14 TelcoSecDay and at the time to me this looked like very solid research. I’d be hence quite interested to hear which of the results can’t be reproduced (as Peter mentioned). This is the newer presentation (“Measures against DNS cache poisoning attacks using IP fragmentation”) from the recent OARC30 meeting which provides a research overview.
His second point – which in itself has some validity – produced a bit of a smile on my side. Put simply: once certain bodies (specific working groups at the IETF come to mind) keep ignoring real-life problems induced by standards they’ve produced, one might not be surprised that at a particular point operators who suffer from said problems in their daily operational life take action, right?
Slides of DNS Flag Day talk here, video here.
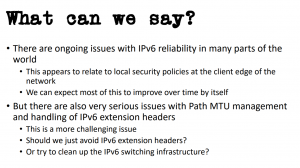
In the IPv6 working group on Thursday Geoff Huston provided very interesting “IPv6 Reliability Measurements” results.
He noted that in some dual-stacked networks the use of Happy Eyeballs (“HE”) as of RFC 8305 effectively masks IPv6-related problems as they might get unnoticed which in turn in the long term can be detrimental to the objective of deploying IPv6 on the Internet scale. He also mentioned that once the routing/upstream paths for v4 and v6 are different, then the resulting round-trip time (RTT) difference might be(come) so big that HE does not even help/kick in. He illustrated that discussing a Vodafone network in the APAC region which has a mostly direct IPv4 connection to Singapore (where, iirc, the servers performing the measurements actually sit) whereas the IPv6 traffic is routed through the UK.
Finally concluded his talk with this slide which I’ll get back to at another occasion soon:
This was followed by Chris’ and my talk on “IPv6 in Wi-Fi Hotspots”. Slides here, video here.
In the afternoon Ignas Bagdonas gave a great “Technology Deep Dive on Modern Router Architectures”. I learned a lot in this one and I highly recommend watching it. Slides here, video here.
Please apologize that I can’t refrain from mentioning that this one had initially been given at IETF104, based on the observation that participants of the 6man working group seemed to have an insufficient understanding of how modern router work (this pic is from the session transcript):
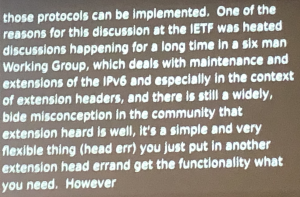
Some readers might guess that I have some particular thoughts on this…
Overall it was an intense week with good technical conversations and exchanges. We might be biased but we furthermore had the impression that there’s a lot momentum in the IPv6 space nowadays.
Everybody have a great Sunday and safe travels! to those of you who’re still in lovely Iceland,
Enno