Niklaus, Manuel and me had a great time speaking about one of the latest Tablet PCs from DPRK at 33C3 this year. Our work on RedStar OS from last year revealed a nasty watermarking mechanism that can be used to track the origin and distribution path of media files in North Korea. We have seen some interesting dead code in some of RedStar’s binaries that indicated a more sophisticated mechanism to control the distribution of media files. We got hands on a Tablet PC called “Ul-lim” that implemented this advanced control mechanism.
The Tablet PC is based on an Allwinner A33 SoC from a Chinese manufacturer and is based on Android 4.4.2. DPRK has developed a bunch of interesting applications, like a full blown office suite that is able to create Microsoft PowerPoint, Word and Excel documents as well as documents based on OpenOffice. It comes with a lot of dictionaries and games pre-installed.

There are no interfaces available that enable communication like WiFi or Bluetooth. All of the classic interfaces must be attached via USB and then enable the Tablet to use external WiFi dongles, Modems and LAN adapters. It is even possible to receive DVB-T that seems to be protected by encryption. DPRK sells this as a feature to protect the users from external DVB-T broadcasts.

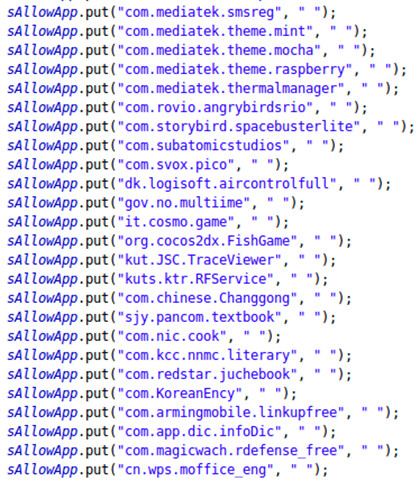
Looking at the available Certificate Authorities it is no surprise that all of them a controlled by the government. Intercepting SSL traffic is therefore easy and usery should be aware that SSL usage from within DPRK does not provide the expected security and privacy. The system itself also does some integrity checking and contains a white list of applications that can be installed. Interestingly the white list also includes games such as Angry Birds or Robo Defense, probably yielding copyright violations. The next picture shows a part of the list with allowed applications.
Browser history and opened applications are logged by a service called RedFlag in the background. The user is able to see the data that the service has gathered but is not able to delete any of it. This is a clear message to the user stating: “We see what you did there …”.
The Tablet is pretty much hardened to provide a high level of integrity for the system and chances are very low that a normal user is able to bypass any of the restrictions DPRK has built into the system. It is also not possible to open arbitrary files on the Tablet. Woolim implements a very restrictive mechanism to prevent the distribution of media files
within DPRK. Based on RSA file signatures the Tablet PCs supports two different ways of signing:
* NATISIGN: Files approved and signed by the government.
* SELFSIGN: Files created and signed by the device itself (e.g. camera pictures, office documents, etc.).
Controlling the signatures gives the DPRK’s government absolute control over media sources. All media files that have not been created by a device itself have to be approved and signed by the government, or various Woolim apps will refuse to open those files. The following picture illustrates the control over Woolim’s media sources:

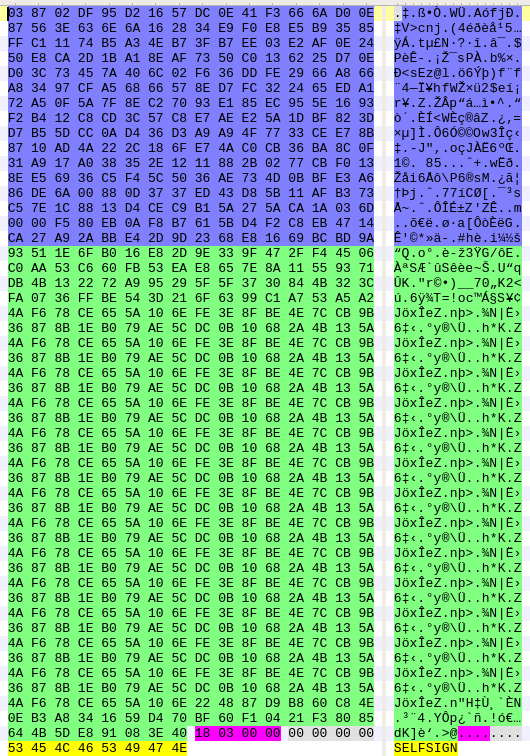
The SELFSIGN signatures are a mixture of various cryptographic algorithms for symmetric encryption, asymmetric encryption/signing and hashing. The SELFSIGN signatures have a fixed size of 792 bytes and have a structure very similar to a custom file format. The first 256 byte are a RSA signature of the SHA256 hash of the file where the signature is appended. The next 520 bytes are encrypted (Rijndael 256) and include some information, most notably a legal reference comprised of the IMEI and Android ID of the device. This reference allows to identify a Woolim device in the DPRK. The trailing bytes include just a length field and the ASCII string “SELFSIGN”. The following picture shows the different areas in a signature.
With this device DPRK has put a lot of effort to provide a strongly restricted Tablet PC for which media distribution can be controlled in a very effective way.
If you can provide us more technology from DPRK to look into, feel free to reach out to us!
Cheers,
Niklaus, Manuel, Flo