Last week we enjoyed quite a wonderful HAXPO exhibition and HITB conference in Amsterdam. A number of great talks could be heard at the main HITB conference such as “Bootkit via SMS: 4G Access Level Security Assessment” or “Stegosploit: Hacking with Pictures“. And not only that: there were also several engaging hands-on workshops.
Apart from the main conference, there was the HAXPO – a hacker exhibition. At this exhibition you could connect with people from different companies, get a lot of merchandise, and also listen to several briefings on security and its philosophy. Fortunately, we had the pleasure to present two of these briefings and maybe you tested your web application skills at the ERNW booth.
In our briefing with the title “When You Stare into the Sandbox, It Stares Back at You: Evaluating the APT Armor” we talked about recent and major Advance Persistent Threads (APT), the promises of certain vendors to defend you against such APTs, and the validity of these promises. If you have missed our briefing, you can find the slides here.
Jayson and Rafael gave their presentation on Pentesting in the age of IPv6. They talked about what you need to know to pentest IPv6 enabled systems and that this is not the same as in IPv4. The importance of this talk in a way is that IPv6 is much more complex than IPv4 and that you have to think and go the IPv6 way. Additionally we recommend you to take a look at some slides of previous IPv6 Blogposts.
The material can be found here:
- Slides
- Tools (the main tool used was Chiron, authored by Antonios),
- IPv6,Complexity
- MLD and complexity
- IPv6 hardening Windows-Server
- Linux Server
- Penetration testing tools that do not support IPv6
- IDPS evasion
Some words from our interns about HAXPO:
First of all, it was a very good opportunity for us to go to HAXPO. Beautiful place, interesting event and the most important, a new experience. Working in the booth helped to develop our soft skills. It was a good training on how to deal with the people coming to us – answer their questions and lead them through the challenges. There were a lot of amateurs who needed guidance and explanations regarding our HackIt challenge and also some advanced guys who used their own techniques.
Although the name infers that it is a Hacking exposition, or an exposition about security, the companies’ activities there were not only limited to security, but there were other branches of IT as well. Some companies had booths while others (which seem as small sized companies) just presented their products on tables. Besides companies advertising themselves or selling products (from t-shirts to hardware) there were a lot of things to look at or even to try. Overall, it seems that there were more hardware products than software services, as the majority of the companies tend to sell their products on the spot. There was also a section of start-up companies, which is very helpful for the young talented people. Also most of the companies there were Dutch, but there were also companies from USA and Singapore. Finally, we feel in general that it was a great chance for us as interns to see and live such experience with really friendly and amazing people.
In addition to HAXPO some of us did attend the HITB conference which was once again very nice. In the following you can find the summaries of the talks:
“#root via SMS: 4G access level security assessment”
by Kirill Nesterov and Timur Yunusov
After reading the talk description we were very excited, here´s a cite:
“In some cases we managed to attack SIM-cards, “clone” phone and intercept traffic without boring rainbow tables, we were able to remotely update USB modem firmware and even gained access to the internal backbone network of the carrier”
They presented their results on this work and it was astonishing to see what they found out.
At first Kirill and Timur gave a short introduction to 4G networks. Radio access is well researched, referring to Karsten Nohl, so they focused on mobile equiptment, SIM cards and Radio/IP access networks. The motivation for their work is that practically everyone of us is using 3G/4G and they wanted to test the security of the access level for these technologies.
Just by using SHODAN they found and got access to several telcommunication provider devices to play around with. Furthermore they said: “If an attacker knows the private APN name he can get inside the telco provider network. They showed how they gained access to an Find Alcaterl SR 7750 and were able to extract a lot of information like APN names and from there on explore the connected networks.
As a second scan technique they sent GTP protocol messages to ports and waited for devices to respond. Their further investigation ended up in being able to mount GPRS attacks (DoS, info leaks, fraud and APN guessing). Though providers block TCP traffic going outside it is possible to connect via UDP VPN as a side channel. They also inspected client devices like 4G-USB-sticks providing the user with the capability to interact with provider services over web dashboards.
As a first demo they showed an XSS included in an SMS sent by an attacker which was triggered when shown in the web dashboard. This leads to several other attack vectors like bricking the device by altering the configuration or just entering the PUK of the SIM wrong the make it unusable via CSRF attacks. They said it is also possible the tamper with these settings to intercept traffic or spy on subscribers or send USSD codes.

For the second demo they modifyed a huawei 4G dongle which was detected as a “bad” usb keyboard starting to attack the system. They were able to completely change the firmware of the device.This again introduces a lot of interesting attack vectors. Then they went on to SIM cards. They have different applications running on the SIM card which can be accessed by the means of binary SMS. The Identifier for accessing such applications is TAR (Toolkit Application Reference). To access these, keys are required which either can be acquired by using rainbow tables or by good old cracking.
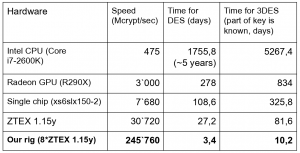
So they build the RIG; a FPGA 3DES cracking device to bruteforce the required keys. After that they were able to send some well known and random commands to well known applicaitons. They also said that Telco Operators can access you SIM card by means of binary SMS. “Mailicous” binary SMS could be filetered out but there are several verctors to circumvent filtering. PINs often require bruteforceing: Pin is often set to 0000 otherwise need bruteforcing.This can also be used as a subscriber DoS over the AIR (pin PUK entered wrong.) They also stated that by acquiring the TMSI and Kc there is no need for kraken any more.
In their third video demo they triggered a call from a victim phone to an attacker phone and later on showed how they clone a SIM card.
In the fourth video demo they intercepted data traffic with wireshark and osmocom to get a look on exchanged SMS. Additionally they showed that only 14 SMS are necessessary for denial of service of a subscriber by just bruteforcing the PIN and thus locking the SIM card. And only 3 SMS were enough to take over control over you victims browser. The researchers also made some recommendations: When talking about mitigations the researchers supposed the application SIMTracer to find out whats going on your SIM card and always changing the default PINs.
For users:
- Change PIN
- Pigeon mail anyone?
For telcos:
- Scan the internet four your devices and restrict access accordingly.
- Subscribers network is not your private nework.
- Do not try to reinvent the wheel/webserver for 4G sticks
- All your 3/4G modems/routers are belong to us
- Check your SIM Cards
- Train your contractor of SIM/App/Sec
For Everyone: PRAY!
Grab the slides here
Shodan founder John Matherly (Grab slides here) started with the keynote on day two where he gave a detailed overview about what one can do with SHODAN. Especially when it comes to the Internet of Things (IoT) he showed some very interesting statistics SHODAN is able to raise. Currently there are discussions about the legitimacy of such large-scale internet scans going and if they violate privacy. For more information on this topic follow these links twitter: @EnnoInsinuator, “Oxford-Workshop”
Non-Hidden Hidden Services Considered Harmful: Attacks and Detection
by Filippo Valsorda and George Tankersley
Afterwards Filippo Valsorda and George Tankersley gave a talk about Security aspects of TOR Hidden Services. In the beginning they introduced the audience to the basics of the TOR protocol and its inner workings, for example establishing a circuit.
The researches claimed that by using a TOR hidden service it is easier to detect users through correlation attacks on entry and exit nodes than by accessing a SSL secured site via the TOR network. But both entry and exit nodes are monitored and secured by the TOR operators. This is a known problem but it can be solved by permanently
monitoring the nodes, which is done actively.
Sooooo what else could happen?
TOR Hidden Services rely on a Hidden Service Directory (short: HSdir).
The TOR Project defines Hidden Service Directories as follows: “HiddenServiceDir is a directory where Tor will store information about that hidden service. In particular, Tor will create a file here named hostname which will tell you the onion URL. You don’t need to add any files to this directory. Make sure this is not the same directory as the hidserv directory you created when setting up httpd, as your HiddenServiceDir contains secret information!” (Link)
To become such an HSdir there are some requirements by the protocol itself. One of these requirements is that the node has to be online for over 4 days.
The attack is based on the fact, that different information is needed to calculate the .onion link. Furthermore the attacker can set up his own Hidden Service Diretory. The combination of these two aspects allow two pretent and a brute-force attack of a specific .onion link, allow to host a Hidden Service Directory for a specific Hidden Service. The results of their attack was, that they controlled 4 out of 6 .onion links of the Hidden Service provided by Facebook.
A solution for this problem would be the new proposal #224 Next Generation Hidden Service. Another solution would be, that the providers of a Hidden Service host their own Hidden Service Directories which makes a detection of such an attack more easier.
Grab the slides here
Stegosploit: Hacking With Pictures
by Saumil Shah
After a short and quite interesting introduction how to hide your malicious code inside a picture using steganography he switched over to how to access the exploit code in a smart way. The first not so smart way is just using a Java Script code on the site and access the image for code extraction. But in his words: “This has no style” The second way in his words “A good exploit is one that is delivered with style” he puts the HTML and Java Script code inside the pictures (JPEG, PNG e.g.) and uses the crazy behavior of the IE or FF browser to just interpret any found HTML code stuff in a file. So you have your exploit and HTML/Java Script code in one handy file. And for a IDS/IPS or Anti Virus solution it just looks like a picture. Great Demos, awesome technique and a lot of fun hearing Saumil´s talk!
Grab the slides here
“µMIMOSAWRITERROUTER: Abusing EPC on Cisco Routers to Collect Data”
by Joaquim Espinhara and Rafael Silva
In their talk Rafael presents a way to abuse a default feature of Cisco routers to configure a remote sniffer using the EPC feature.
He starts with an introduction to EPC on Cisco Routers and explains what it is about. The Cisco IOS Embedded Packet Capture (EPC) is a troubleshooting and tracing tool with the ability to capture IPv4 and IPv6 packets. It can be used to sniff data on the fly, however it has limited options to analyze the data, he says. To circumvent this limitation, he uses the facility to export the packet captures in PCAP format to a remote location over scp, ftp, https & more. In his opinion, the main problem is the export of the captures to a REMOTE location and there is no way to disable the EPC or block the export to a remote location.
After the introduction to EPC, he presents their Framework Mimosa. Mimosa is an automated tool to help pentesters to collect data in a controlled environment abusing EPC on Cisco Routers. Next, he shows their approach using Mimosa: they use µMimosa C&C to control the routers and send the data to collectors with the µMimosa Parser they are now able to extract all kind of data like ftp, pop credentials, exctract cookies & more.
He finished his talk, with some information about the future development of Mimosa.
You could get Mimosa from following GitHub page:
We are looking forward to see you at the next HAXPO/HITB!
Have a safe day,
Your ERNW Team
