In a .NET environment WCF services can use the proprietary WCF binary XML protocol described here. Microsoft uses this protocol to save some time parsing the transmitted XML data. If you have to (pen-) test such services, it would be nice to read (and modify) the communication between (for example) clients and servers. One possibility is Fiddler.
Fiddler’s strengths include its extensibility and its WCF binary plugins. Sadly, these plugins can only decode and display the binary content as XML text.
Our first tool of choice for webapp pentests (Burp Suite) has also a plugin feature, and one can also find plugins for decoding (and encoding XML back to) WCF binary streams. But all WCF binary plugins out there are based on the .NET library which means one either has to work on MS Windows or with Mono. Another disadvantage is the validation and auto-correction feature of such libraries… not very useful for penetration testing 😉
That’s why we decided to write a small python library according to Microsoft’s Open Specification which enables us to decode and encode WCF binary streams. The library has a rudimentary commandline interface for converting XML to WCF binary and vice versa, as well as a plugin for our python-to-Burp plugin (pyBurp).
The commandline interface consists of two python scripts:
| Script | Description | Examples |
| wcf2xml.py |
|
./wcf2xml.py example.bin./wcf2xml.py < example.bin |
| xml2wcf.py |
|
./xml2wcf.py example.xml./xml2wcf.py < example.xml |
In combination with our python-to-Burp plugin (pyBurp) you can decode, edit and encode WCF-
Binary streams on the fly.
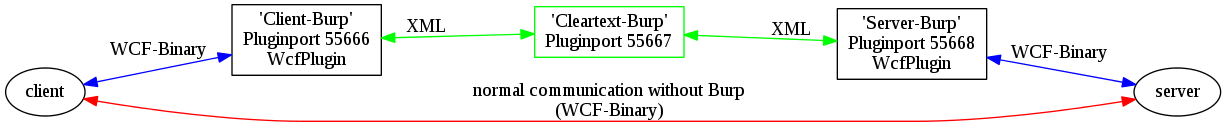
At the moment you’ll need three Burp instances to use all Burp features. The first one (“Client-Burp”) decodes/encodes the data from/to the client. The second one (“Cleartext-Burp”) operates on the
XML like it was a normal request/response. The third one (“Server-Burp”) encodes/decodes the data to/from the server.
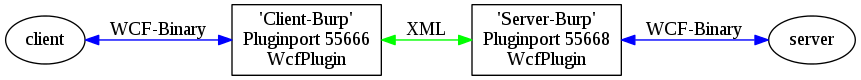
A setup without the “Cleartext-Burp” is also possible, but we experienced problems in combination with some Burp features like auto replace.
We are currently working on a one-Burp-solution, but we’ll have to understand the exact communication flow inside of Burp first and how we can interact with it (without breaking some things).
After setting up pyBurp, one only has to connect to the current Burp instance, change the current root directory to the path were pyWCFBin is located and then load the WcfPlugin:
$ nc localhost 55666 cd /home/foo/Downloads/pyWCFBin add WcfPlugin quit $
The pyWCFBin plugin must only be used on the Client-Burp and Server-Burp.
Downloads:
- Sourcecode: pyWCFBin.tar.gz
- SHA1: c60f9f52c735e750a35b19cda6b99c7ad6d5742a
- MD5: 4b00f82cfee686c5886a9e1ed93bdc48
We hope some of you find this library useful when working with WCF Services. We’re happy to receive any feedback or bug reports in case you find some 😉
Merry Christmas and a happy new year to everybody
Timo
Hi,
it sounds really great, however, before I start playing around with it, could you specify which bindings are supported. I am actually looking for a solution to work with NetTcpBinding, however, I am afraid that you are talking about BasicHttpBinding with encoded XML. Is that correct? If so have you any suggestions for NetTcpBinding, because I am afraid that burp wouldn’t understand it anyway (since it is not HTTP).
Thanks!
Geri
Hi geri,
first of all, the library enables you to transform WCF binary XML into normal, textdriven XML and vice versa. So as long as the nettcpbinding uses the same encoding scheme as the *httpbinding and you capture the traffic you should be fine. Till now I’ve only written a plugin for burp, so automatic encoding/decoding is only available within the capabilities of burp. But you are free to use the library with your own python scripts.
Maybe you like to hear that it’s now on github: https://github.com/bluec0re/python-wcfbin
(Therefore improvements or fixes can be better included)
Thanks and take care,
Timo
Hi Timo,
ok, great thanks. I will try it out :).
All the best,
Geri
You’re the best, great thanks for your article, very useful to me.